Subscribe to our blog
Thanks for subscribing to the blog.
February 27, 2015
Topics: Cloud Volumes ONTAP 4 minute read
In the other Getting Started with AWS posts I discussed various aspects of AWS account management - Creating an AWS Account, IAM Users & Groups, as well as rolling up your charges with Consolidated Billing. All very useful aspects for ensuring your account is established and set up the way you want... but not really telling you what you need to know for doing things in AWS.
This doing things in AWS is something I usually refer to as AWS Basics. What are the first things you need to know in order to start deploying things and connecting to virtual machines in your AWS account? As for basics... I break them down into two key areas:
- AWS Networking
- AWS Virtual Machines
While our end goal is to really focus on our Virtual Machines, we really need to first understand how we will be connecting to those Virtual Machines, or at least understand more around AWS Networking. If we don't then we might be signing up for a lot of frustration. With that in mind... let's Get Started.
AWS Basics: AWS Networking – VPC (Virtual Private Cloud)
If you have already gotten started and accessed your AWS console you'll see there a lot of available options... and this holds true for AWS Networking as well. While there are other AWS Networking components, the right place to start is with your AWS VPC (Virtual Private Cloud). We'll dive deeper into the other aspects of AWS Networking in future posts.
First, let’s start with a definition. I can't take credit for this since AWS provides some absolutely excellent online documentation on VPCs, so here is their definition:
"Amazon Virtual Private Cloud (Amazon VPC) enables you to launch Amazon Web Services (AWS) resources into a virtual network that you've defined. This virtual network closely resembles a traditional network that you'd operate in your own data center, with the benefits of using the scalable infrastructure of AWS."
Okay... good. This is our AWS Public Cloud network... with all the networking aspects we'll have in our datacenter... and more. This is both good and bad. Good if you're familiar with networking. Not quite so good if you're not. Never fear, this is one of the main reasons for this post... to try and make sense of it all. You will have a ton of options with a VPC, but you’ll want to pay special attention to the following:
Regions and Availability Zones
- Where do you want to take advantage of AWS?
- AWS Regions are completely isolated from each other. Chose one close to you or your resources.
- Availability Zones. Think of these as connected 'sub-Regions'. While each AWS Region is isolated, there are multiple Availability Zones (or AZ) within a Region that are connected to each other low-latency links.
- There are many ways to configure your AWS networking:
- Tightly locked down and secured (recommended)
- Fully open and public
NOTE: For learning purposes I do suggest starting with this type of VPC until you feel comfortable with the networking security options. This removes any initial roadblocks you might run into when you are first trying to see how things work - Somewhere in between
- A Subnet lives with in a VPC and within a single AZ
- You can have multiple Subnets within a VPC that live in different AZs
- This enables you to access the Internet... it also enables things on the Internet to access you!
- Can your resources actually 'talk' to each other? Don't assume that your Route Tables will be there by default... or propagated by default. If you can't connect... check. Some of AWS' VPC wizards really do help in this regard
- This is effectively your AWS Firewall that restricts/grants access to and from your AWS virtual machines. We also have a post going deeper into Security Groups in our Demystifying Amazon Web Services series if you want to dive right in and find out more
Is that all? Nope, not by a long shot... but we'll cover several of the other AWS Networking aspects in future posts.
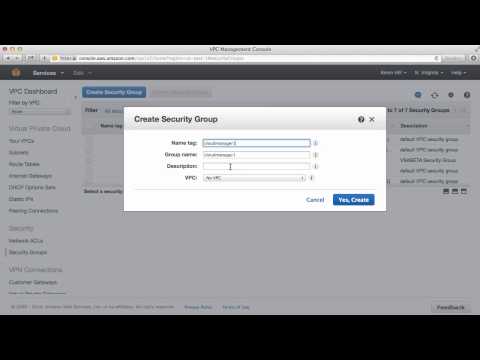
Hopefully what I've laid out above helps you learn a bit more about your AWS networking. Also, to assist you even more with learning about your AWS networking we have a short video that shows you how to create a new VPC with a public Subnet and a fully open Security Group. While we don't recommend this configuration for live usage, it does allow you to get up and going quickly to try things out.
Watch the video now
Now… if you followed along with the video, you just created a PUBLIC AWS network and an OPEN AWS firewall. I have two things to say:
- Congratulations! You're in the Public Cloud
- Now... NEVER do that again!!! Strap some security around yourself!
There are actually some reasons for having something publicly accessible and easy to use. That said, you should have some good practices around that configuration, and fully understanding your exposure.
Everything we've discussed in this post refers to your AWS networking. Now that we understand a bit more about that we can start looking at our AWS Virtual Machines. We'll dive into that topic in our next post.
Check back soon!